Have you ever paused at a message that sounded exactly like a co-worker, and then noticed something slightly off? Vibe Hacking takes that same idea and scales it with AI. Attackers use models to write believable messages, create small scripts, and run steps automatically so the activity blends into normal operations.
Vibe Hacking is different from ordinary social engineering because it combines those believable messages with automation and quick code changes. Instead of one crafted message and manual follow-up, attackers can produce many variants, test which ones work, and then trigger automated follow-ups that look routine. That combination makes detection harder and lets campaigns move faster.
What Vibe Hacking Means
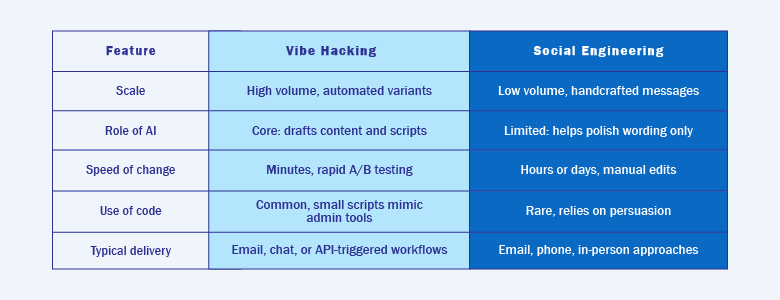
Vibe Hacking builds on social engineering but adds automation. A human still guides the campaign, yet AI speeds up writing, testing, and scaling. This means attackers can tailor messages to local details like payroll cycles or remittance services and then run follow-up actions with minimal manual steps.
The important difference is scale and adaptability. Where social engineering relies mainly on human effort, vibe hacking mixes human context with automated processes and quickly changing code. That creates attacks that are both believable and repeated at scale, which is why defenders need to treat them differently.
How Attackers Use AI in Vibe Hacking
AI helps in two main ways: content generation and workflow automation. For content, models craft messages that use local names, dates, and common business processes so the lure feels genuine. For automation, simple agent workflows can sequence reconnaissance, delivery, and execution so the attack flows without constant human input.
Combining these capabilities lets attackers test many message versions and refine scripts until the activity looks normal in logs. This ability to iterate fast is what gives vibe-hacking campaigns an edge over traditional phishing or manual scams.
Recent reporting and vendor advisories show this is not just theoretical. Security researchers and companies have documented misuse of commercial models, including Anthropic’s Claude, where attackers used the model to draft highly tailored lures, generate code snippets used in extortion and ransomware, and automate parts of intrusion workflows. Researchers have also observed fake downloads and prompt-injection techniques that try to trick users into running malicious code or leaking credentials. These cases underscore why defenders must treat model misuse as a practical threat, not just a research concern.
Why Signature-Based Defenses Often Miss These Attacks
Defenses that look only for known malicious files or fixed patterns struggle when payloads and messages change rapidly. AI-generated scripts change content and structure, so hash-based checks and static signatures lose effectiveness. At the same time, attackers often reuse legitimate admin tools, which makes the activity resemble normal IT work.
As a result, defenders need to shift focus from single-file detection to context and behavior. Watching sequences of actions, unusual combinations of otherwise benign tools, and unexpected outbound connections gives a better chance of spotting vibe-hacking activity.
Real-World Signals and Local Examples
Vendors and researchers have started to document incidents where AI-assisted campaigns combined believable lures with scripted actions. Picture a finance staff member receiving an invoice email that mentions a local remittance provider by name, followed by a link that triggers a small script mimicking routine file handling. The message lowers suspicion and the script hides in everyday operations.
In the Philippines, common triggers include payroll notices, remittance confirmations, and supplier invoices. These are practical hooks attackers use because people expect them. Not every suspicious message is an attack, but small differences combined with unusual downstream activity are the signals teams should watch.
Four Practical Next Steps for IT Teams
These four steps are short, focused projects your team can complete quickly. Scope each as a one- or two-week task, assign an owner, and set a simple success metric so progress is visible.
- Increase visibility into administrative tools and automated tasks. Turn on or expand logging for admin consoles, scheduled jobs, and remote sessions. Capture who ran commands, when they ran them, and basic command parameters, then set simple alerts for spikes in activity or scripts run by unexpected accounts.
- Enforce multi-factor authentication for privileged accounts. Require MFA for any account with elevated access, track adoption, and start with the highest-risk users so you get fast, measurable protection.
- Reduce service account privileges and rotate credentials regularly. Create an inventory of service accounts, assign a named owner to each, remove unused accounts, and roll keys or passwords on a schedule so long-lived credentials do not become a silent risk.
- Run short, phishing simulations and follow-up drills. Use realistic lures delivered through a controlled channel, measure reporting rates and time-to-report, and check whether automated protections block the test. Use the findings to tune alert thresholds and improve incident response steps
If your team prefers outside support, a Managed Security Operations Center can strengthen detection and response. A managed SOC continuously monitors logs and telemetry, correlates events across systems, and helps surface subtle sequences of otherwise normal actions that may indicate vibe-hacking activity. This makes it easier to prioritize alerts and focus on remediation and governance decisions.
Complementing monitoring, vulnerability assessment and penetration testing produce prioritized findings that show where to harden systems. CT Link offers monitoring and testing services that support your team without replacing internal policy or decision making.
Interested in learning more about how you can keep yourself safe from Vibe Hacking? Explore our different security solutions or consult with us today!

